Who Is Paul Tracey And Why Is Everyone In
Cyber Security Talking About Him?

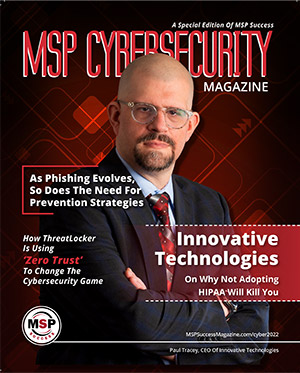
Paul Tracey, President
A History Of Stopping Security Breaches & IT Problems BEFORE They Happen For SMB’s
Paul Tracey was infuriated that lazy, unresponsive and inept IT personnel and companies were leaving small businesses vulnerable to cyberattacks that would cost them everything. In 2012, he founded HIPAA-verified Innovative Technologies as a full-service managed security service provider to help small and medium-sized businesses mitigate cybersecurity risks and establish a company culture that supports secure and efficient IT.
Prior to starting Innovative Technologies almost 10 years ago, Tracey talked to local business owners to gauge their IT and cybersecurity awareness. What he heard shocked him. There was an attitude that security hacks and data breaches only happened to larger, high-profile companies. They were not aware of the risks and responsibilities that exist around their data. The threat did not seem real to them; they did not anticipate that an employee clicking on the wrong link could shut down their company.
Amazon #1 Best-Selling Author on Cyber Security
Contact Paul
How Disaster Inspired Paul Tracey’s Unmatched Security & Compliance Plan
Paul Tracey was a pressman in the printing industry when the unthinkable happened: a devastating shoulder injury disabled him from ever working in manual labor again.
Forced to find an alternative source of income, Paul pursued his tech obsession he’d developed growing up and went back to college. “I always was fascinated with how computers work and how the code could be manipulated,” he said. “In high school I’d program simple video games into graphing calculators. With the arrival of the internet, my curiosity exploded, so it seemed logical to do what I loved.” After graduating from college in 2009 with his network administration degree, he managed an outsourced IT help desk call center with 300 to 400 employees.
But his education for how technology was REALLY being handled started when he went into IT support for a major hospital. Quickly promoted to an Operation Specialist, he was stunned the first time he saw the ugly side of how big corporations were handling IT security and compliance.

Why Your Customers Need To Adopt A HIPAA Mindset
Every morning, when Paul Tracey, founder and CEO of Innovative Technologies, wakes up, he’s greeted with a new list of cybersecurity threats.
The morning we spoke, one of Tracey’s clients had an employee who downloaded a document at their home, uploaded it to their Google Drive, then downloaded it again when they got to work. Loaded with malware, the document put the client’s company in danger. Fortunately, because of the procedures Tracey has in place, his team discovered the document immediately and ended that threat within 35 seconds from when it started. But for many companies that don’t have a cybersecurity plan in place, this wouldn’t have ended so well.
Tracey realized early in his IT career that companies were grossly undereducated and unprepared for cyberthreats. Therefore, for over a decade, Tracey has been on a mission to educate SMB owners whose livelihoods are at risk by what they don’t know about IT and cybersecurity threats. The author of “Delete The Hackers Playbook” and co-author of “Cyberstorm” (due to be released in 2022), he started his own company after witnessing a large hospital pay hefty fines when their lax security caused a major breach. Realizing that “cybersecurity inequity is highly problematic,” Tracey dedicated himself to fighting cybercrime for the business owners who are the most vulnerable. Today, he helps businesses establish a company culture that supports safe, secure, and efficient IT.

Paul’s Top Areas Of Expertise
- Cyber Security
- HIPAA Compliance
- NYS Shield Act
- NYS Education Law 2.D
- Disaster Recovery and Business Continuity
- Microsoft Partner
- Author with 2 Amazon Bestsellers
As a leader in the information technology and Cyber Security expert and Owner of Innovative Technologies for over a decade, Paul has helped SMB's experience extraordinary growth, efficiency and increased data protection from security threats across all technical platforms while guiding them on their journey through stages of Cyber Security Maturity. He is a highly sought-after keynote speaker, author of Delete The Hacker Playbook , and co-author of 2 Amazon Bestsellers; Cyber Storm and Compliance Made Easy . He has been featured in various news segments across the United States and online, quoted in articles written by major news publications and industry leading publications, as well as being featured in multiple Podcasts. Most recently Paul has been working on a movie, 'Cybercrime Investigations ', which will had it's L.A premier September 7, 2023.

 Contact Us At
Contact Us At